SOC 2 for AI Companies: Complete Guide (2025)
Your complete 2025 guide to SOC 2 for AI companies. Covers requirements, costs, timelines, and how to achieve compliance in weeks instead of months.
You're in a sales call that's going perfectly. The prospect loves your AI product, the demo went great, and they're ready to move forward. Then comes the question: "So, do you have a SOC 2 report?"
If you've felt that sinking feeling, you're not alone. For B2B AI companies in 2025, SOC 2 compliance has shifted from "nice to have" to "non-negotiable." Roughly 66% of B2B buyers now demand a SOC 2 report before they'll even consider working with a vendor. And when your AI system handles sensitive data (which it almost certainly does), that requirement makes complete sense.

The good news? Getting SOC 2 compliant doesn't have to mean months of painful preparation or burning through your engineering budget. This guide walks through everything AI companies need to know about SOC 2: why it matters, what it actually requires, and how to get it done in weeks instead of quarters.
What You'll Learn:
- Why AI Companies Need SOC 2 Compliance
- What is SOC 2? (And Does It Cover AI?)
- Key Benefits of SOC 2 for AI Startups
- Challenges AI Teams Face Getting SOC 2
- Step-by-Step: How to Achieve SOC 2 Compliance
- How Automation and AI Tools Speed Up Compliance
- How Comp AI Helps AI Companies Get SOC 2
- Frequently Asked Questions
Why Do AI Companies Need SOC 2 Compliance?
If you run an AI company, you've probably fielded security questions from potential customers: "How do you protect our data?" or "What happens to the data we feed your model?" These aren't just formalities. They're deal-breakers.
Here's why SOC 2 has become essential for AI companies specifically:
Your customers handle sensitive data, and so do you.
AI systems typically process massive amounts of information: personal identifiers, financial records, healthcare data, proprietary business content. A single security lapse can destroy trust instantly. According to industry research, 65% of consumers say they would stop doing business with a company after a single data breach. That's not a statistic you want to test.
SOC 2 compliance provides independent verification that your security controls meet industry standards. Instead of asking prospects to just trust you, you can show them an auditor's report vouching for your practices. Studies show 83% of consumers are more likely to engage with companies they believe protect data well. SOC 2 turns your security practices into a competitive advantage.
Enterprise deals require it.
Large enterprises, especially in finance, healthcare, and other regulated industries, commonly require SOC 2 as a condition for partnership. Many corporate security teams won't even look at an AI vendor that lacks a SOC 2 report. You could be excluded from RFPs and proof-of-concept opportunities before you even get a chance to demo your product. For an AI startup looking to sell into enterprises or raise funding, being SOC 2 compliant opens doors that would otherwise stay firmly closed.
Investors see it as a maturity signal.
When investors conduct technical due diligence, they look for signs that your company can scale without falling apart. SOC 2 compliance signals that you've moved beyond ad-hoc security practices into a phase of structured, repeatable processes. It shows discipline. And in an era where even early-stage investors worry about cyber risks, being able to say "we're SOC 2 compliant" can set you apart.
Prevention is cheaper than response.
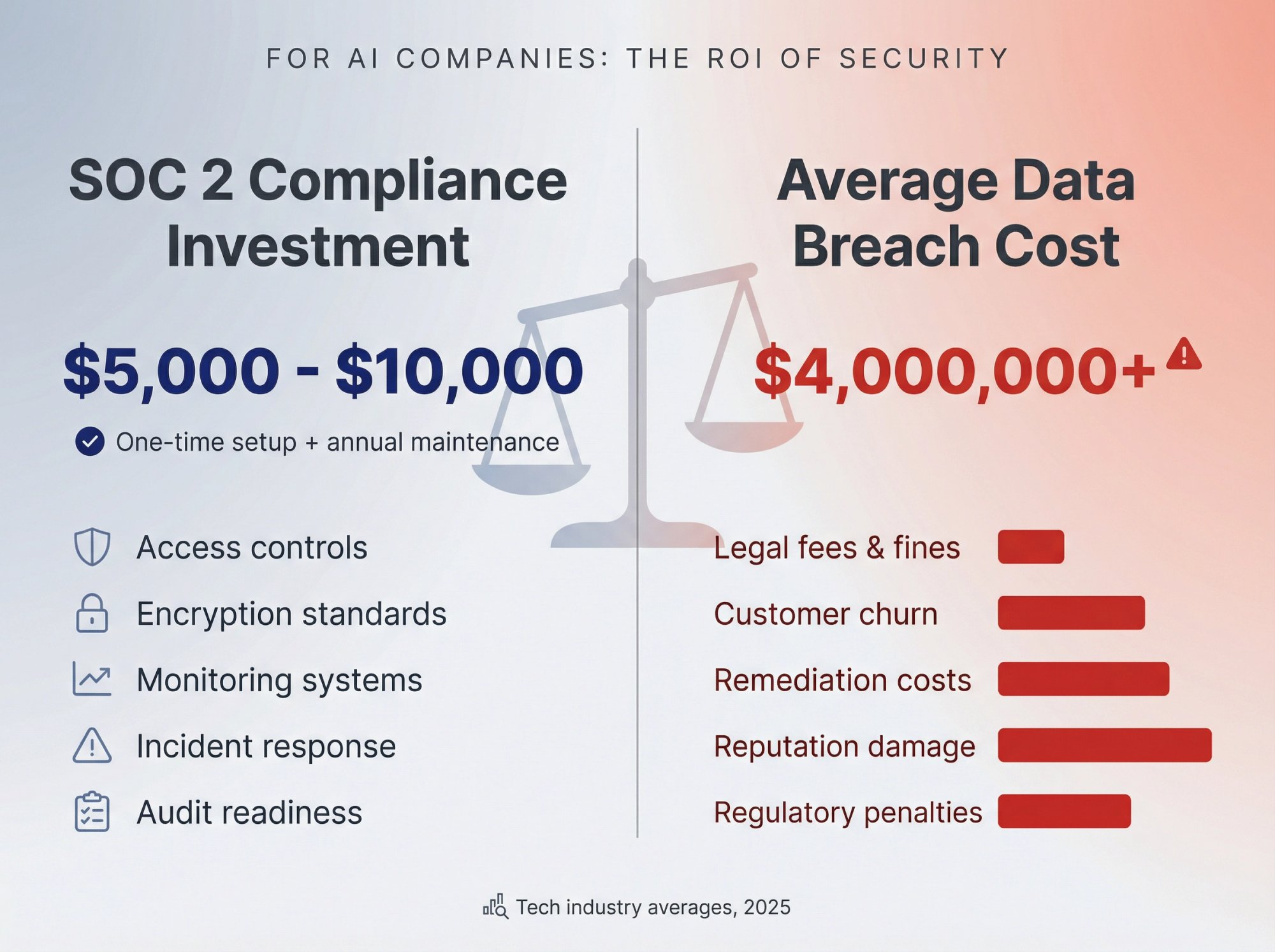
The controls you implement for SOC 2 (access management, encryption, monitoring, incident response) directly reduce your risk of a security incident. The average cost of a data breach in tech companies now exceeds $4 million. The investment in compliance is dramatically cheaper than dealing with a breach. And for AI companies, which often host valuable models and proprietary training data, the stakes are even higher.
Bottom line: SOC 2 isn't just about passing an audit. It's about establishing credibility in a market where trust is everything, especially when your product is an AI system that customers can't fully see inside.
What Is SOC 2 and Does It Apply to AI Companies?
SOC 2 (System and Organization Controls 2) is an auditing standard from the American Institute of CPAs (AICPA) that evaluates how companies safeguard customer data. Unlike a one-time certification, SOC 2 is a report issued by an independent auditor who assesses your security controls against the Trust Services Criteria.
These criteria cover five key areas:
| Criterion | What It Covers | Required? |
|---|---|---|
| Security | Protection of systems and data against unauthorized access | Yes (mandatory) |
| Availability | Systems are operational and reachable as agreed (uptime, disaster recovery) | Optional |
| Processing Integrity | Systems process data accurately and as intended | Optional |
| Confidentiality | Sensitive information is properly restricted and encrypted | Optional |
| Privacy | Personal data is handled in line with stated policies and regulations | Optional |
Security is mandatory in every SOC 2 audit. The other four criteria are optional, and you choose which ones to include based on your business. Most SaaS startups include Security, Confidentiality, and Availability. If you handle personal data extensively, you'd add Privacy.

Does SOC 2 Have AI-Specific Requirements?
Here's something important to understand: SOC 2 does not include any controls unique to artificial intelligence or machine learning systems. It applies to AI companies the same way it applies to any cloud or software provider that handles customer data.
SOC 2 cares that you secure data, whether that data lives in a traditional database or gets processed by an ML model. The auditor will check that access to your model training data is restricted (security control) and that you have backups for critical systems (availability). But they won't ask about model bias, ML explainability, or other AI-specific governance issues. Those are outside SOC 2's scope.
This is actually good news: you don't need some special "AI version" of SOC 2. The same framework that thousands of SaaS companies use applies to your AI company too.
SOC 2 Type I vs Type II: What's the Difference?
This distinction trips up a lot of first-timers:
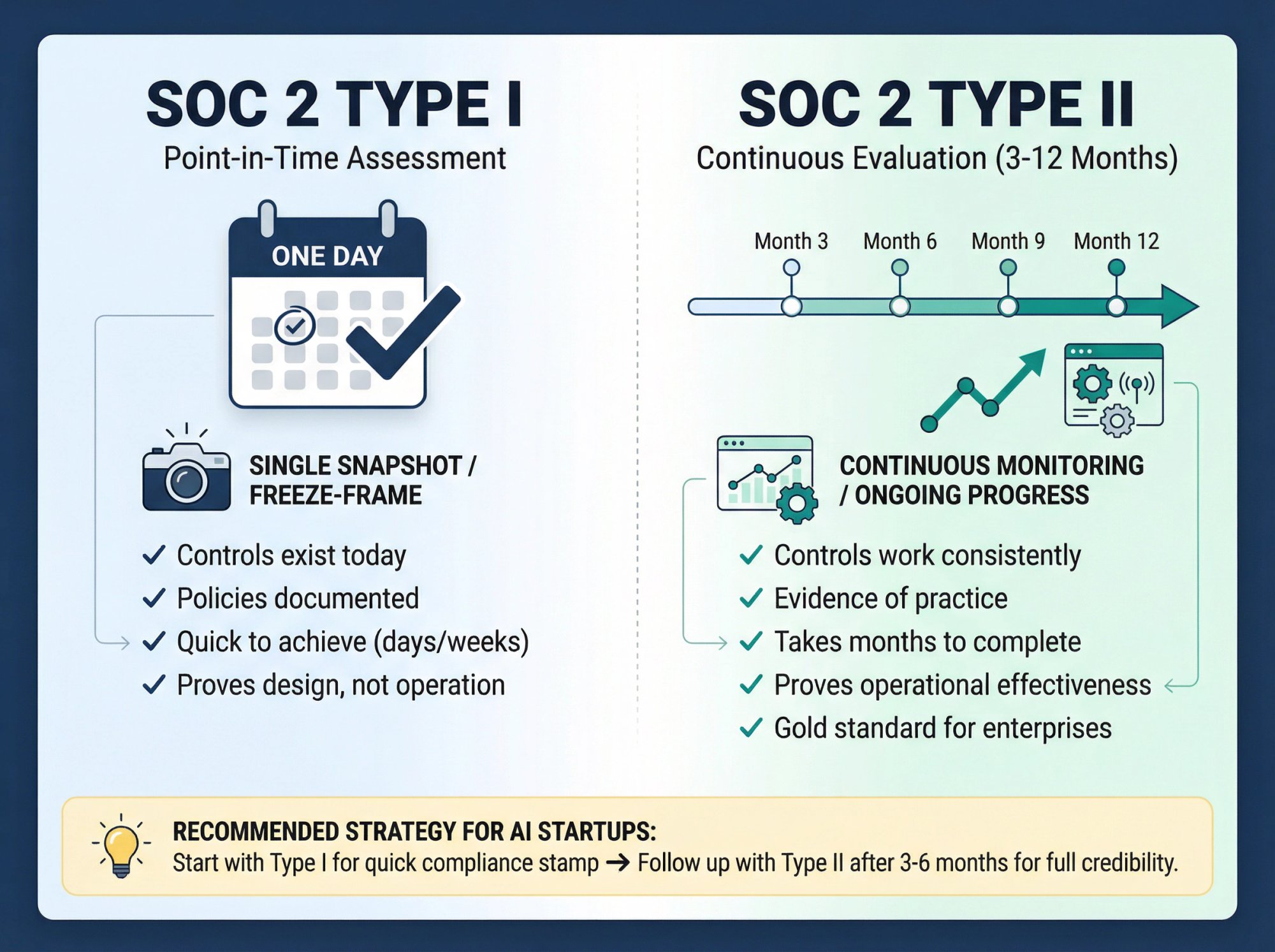
SOC 2 Type I examines your controls at a single point in time. It answers: "As of today, do you have the required security policies and mechanisms in place?" Type I is useful as a first step to prove your controls are in place, but it doesn't prove those controls actually work consistently over time.
SOC 2 Type II evaluates your controls over a period (typically 3 to 12 months). The auditor checks not just that you have policies, but that you follow them in practice: reviewing evidence that you monitored access logs continuously, performed regular backups, responded to incidents according to procedure, and so on. Type II is considered the gold standard because it proves operational effectiveness.
A practical strategy for AI startups: Start with SOC 2 Type I to get a compliance stamp quickly, then follow up with Type II after a few months. This lets you satisfy initial customer requirements while building toward full credibility.
Keep in mind that SOC 2 reports are generally valid for 12 months, meaning you'll need annual audits to maintain compliance. Think of it as integrating security into your company's DNA, not a one-time project.
What Are the Benefits of SOC 2 for AI Startups?
Getting SOC 2 takes effort. But the benefits are concrete:
1. How SOC 2 Builds Customer Trust for AI Companies
SOC 2 provides independent verification that your security controls meet industry standards. For AI companies handling sensitive data, this independent validation is critical. Instead of saying "trust us," you can point to an auditor's report. That changes the conversation entirely.
2. How SOC 2 Unlocks Enterprise Sales for AI Startups
For startups selling AI solutions to large organizations, SOC 2 is often a gating item. Big enterprises, especially in finance, healthcare, and regulated industries, typically require SOC 2 compliance from vendors. Having your SOC 2 ready means you won't get disqualified on security grounds before the real evaluation even begins. You'll pass security questionnaires with far less friction, shorten sales cycles, and expand your pool of potential customers.
3. How SOC 2 Demonstrates Operational Maturity
Successfully completing SOC 2 shows that your AI startup has moved beyond "cowboy coding" and ad-hoc processes into structured, disciplined operations. It proves you have documented policies, repeatable security processes, and continuous monitoring. Investors, board members, and strategic partners value this. It signals you can scale without security becoming a bottleneck.
4. How SOC 2 Reduces Security Risks and Breaches
The security controls required for SOC 2 have real-world benefits. Requirements like access controls, encryption, activity logging, and incident response planning directly lower your odds of a security incident. Enforcing MFA for administrative access prevents account takeovers. Continuous monitoring catches anomalies faster. You're not just checking compliance boxes; you're actually hardening your systems.
5. How SOC 2 Prepares You for Future Compliance
SOC 2's principles align with many data protection laws like GDPR, CCPA, and HIPAA. By implementing SOC 2 controls, you simultaneously lay groundwork for meeting these regulations. When new compliance requirements arise (and they will, especially for AI), you'll already have the foundation in place. Think of it as building the muscle memory for compliance early.
What Challenges Do AI Teams Face Getting SOC 2?
Understanding the challenges upfront helps you navigate them better:
Lack of in-house compliance expertise. Most AI companies are founded by engineers and researchers who know machine learning, not security frameworks or audit processes. SOC 2 introduces concepts like control mapping, evidence collection, and policy documentation that feel foreign. Without someone who's done this before, it's easy to feel overwhelmed.
Time and resource constraints. Preparing for SOC 2 the traditional way can take months and pull key people (your CTO, senior engineers) away from product work. A typical SOC 2 readiness project might involve 100+ hours of assembling evidence, writing policies, implementing tools, and coordinating with auditors. For a lean AI startup, that's a significant opportunity cost.
Rapidly evolving infrastructure. AI startups often have fast-changing tech stacks. You might spin up new cloud instances, integrate specialized AI platforms, or add new datasets frequently. Keeping a continuously updated inventory of systems (which auditors require) is tricky when things change weekly. Each new component needs proper security controls.
Data privacy complexity. AI companies deal with unique data scenarios: customer-provided datasets for training, user data retained to improve algorithms, proprietary model weights. Ensuring proper controls around all of this (Who has access? How is it anonymized? Is client data segregated?) requires thoughtful policy design.
Documentation and process discipline. Startups run fast and informal. But SOC 2 requires documentation and consistency. It's not enough to say "we generally restrict access to production." You need an Access Control Policy document, and you need logs proving you followed it. This means introducing new habits: writing things down, following change management procedures, conducting regular security training.
Maintaining compliance post-audit. SOC 2 isn't one-and-done. You need to maintain controls continuously. For AI companies that iterate quickly, there's a risk that new features or rapid growth create gaps. Building a sustainable compliance program (not just a one-time push) is the real challenge.

The good news: these challenges are solvable, especially with modern automation tools built specifically for this purpose.
How to Achieve SOC 2 Compliance Step by Step
Here's a practical roadmap:
Step 1: How to Scope Your SOC 2 Audit
Decide what you'll include in your audit. This means choosing which Trust Services Criteria apply (Security is mandatory, others are optional) and which systems and processes are "in scope."
For most AI startups: include your production environment, databases, cloud accounts, and the teams supporting them. Focus on parts of your infrastructure that store or process customer data. Your internal R&D tools or marketing website might be out of scope. A word of caution: too broad a scope overwhelms you, too narrow and the report might not satisfy customers.
Step 2: How to Perform a SOC 2 Gap Analysis
Assess where you currently stand versus where you need to be. Review each relevant SOC 2 requirement and check if you have a control in place. Go through a checklist and mark what exists and what's missing.
Common gaps startups discover: no formal incident response plan, never did a vendor risk assessment, MFA enabled on AWS but not on GitHub, no documented onboarding security process. The result should be a clear list of action items.
Step 3: How to Implement SOC 2 Controls and Policies
Fill the gaps. This involves two categories:
Technical controls: Enable encryption on databases, enforce SSO/MFA on all apps, set up logging and alerting for security events, deploy endpoint protection on laptops.
Administrative controls: Formalize your Information Security Policy, Access Control Policy, Incident Response Plan, Backup Policy, and others. Begin practicing procedures like employee security training, regular access reviews, and onboarding checklists.
For AI companies specifically: pay attention to controls around data handling for training datasets and customer data.
Step 4: How to Collect SOC 2 Evidence
As you implement controls, gather evidence to prove they exist and work. This includes:
- Screenshots of security settings (AWS IAM MFA enforcement, GitHub branch protection)
- Policy documents and revision history
- Logs and reports (access logs, incident response records)
- Training records (security awareness completion certificates)
- Asset inventories and user lists
This evidence can be voluminous. Modern compliance management software automates much of it, but either way, organize your evidence clearly and map it to each control requirement.
Step 5: How to Conduct a SOC 2 Readiness Assessment
Before the official audit, do a mock review. Check everything yourself or hire a compliance consultant for a light assessment. The goal is catching gaps before the auditor does.
Maybe a policy exists but employees aren't following it. Maybe your log monitoring was only partially configured. Fix these proactively.
Step 6: How to Choose and Work with a SOC 2 Auditor
SOC 2 audits must be performed by an accredited CPA firm specializing in information security audits. Choose one familiar with startups and technology companies (so they understand cloud infrastructure, CI/CD pipelines, etc.).
Define the scope and audit period with them. For Type I, the audit is point-in-time. For Type II, they'll review evidence over the past several months. Expect detailed discussions about how your controls work, interviews with team members, and sampling of evidence. With good preparation, this process takes a few days of auditor time spread over a couple weeks of coordination.
Step 7: How to Maintain Continuous SOC 2 Compliance
After obtaining your report, operationalize the controls into a regular cadence: quarterly access reviews, annual policy updates, ongoing security training for new hires, continuous monitoring. Prepare to renew SOC 2 annually via Type II audits.
The best approach is treating compliance as integral to operations. Security becomes a habit, not an annual fire drill.
(For more detail on timelines, costs, and best practices, see our companion guide: How to Get SOC 2 Certification: Complete Guide.)
How Do Automation Tools Speed Up SOC 2 Compliance?
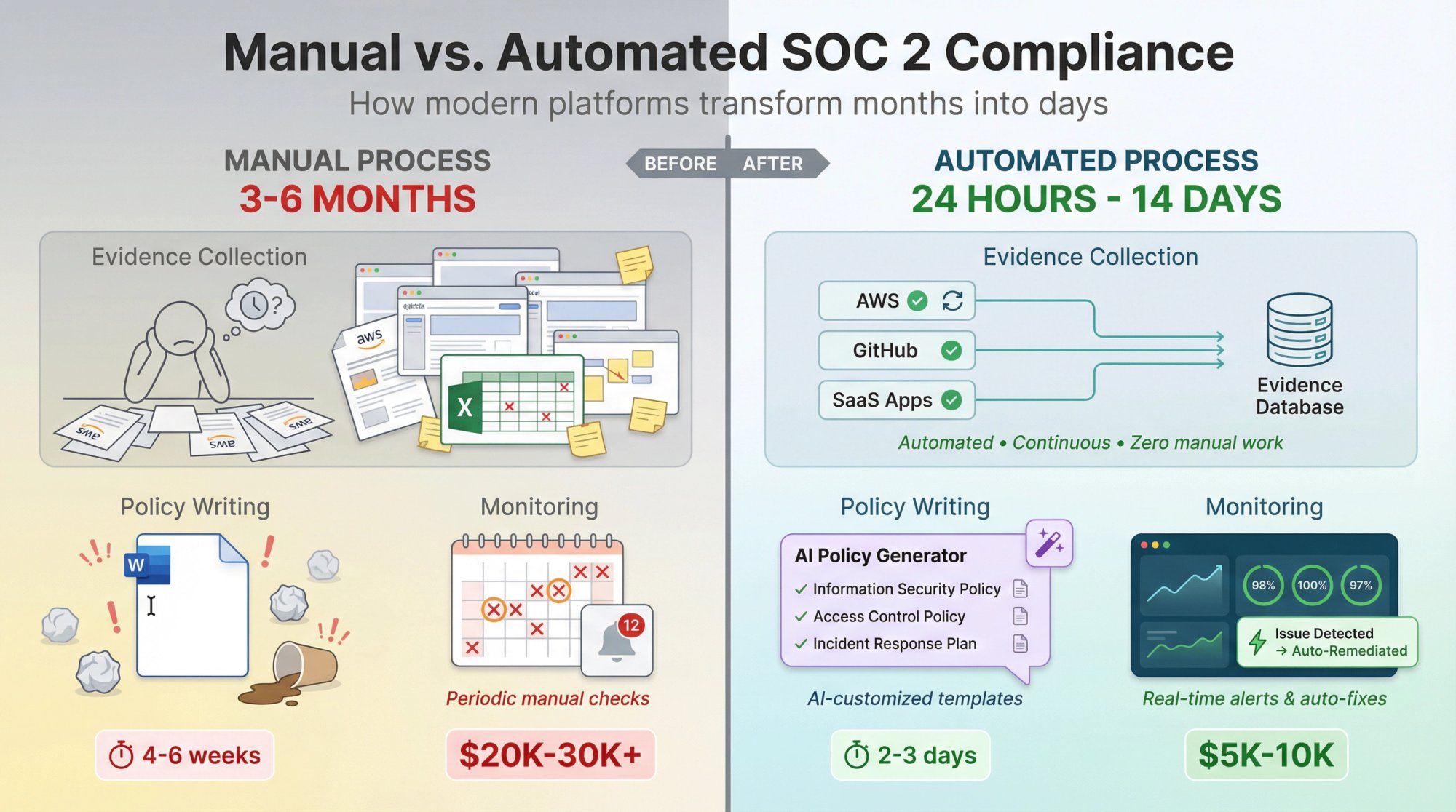
Traditional SOC 2 projects have a reputation for tedium: endless spreadsheets, manual screenshots, document version control nightmares. But a new generation of compliance automation platforms has changed what's possible.
How Automated Evidence Collection Works
One of the most labor-intensive parts of SOC 2 prep is gathering proof for each control. Modern platforms connect to your tech stack (cloud accounts, code repos, SaaS apps) and auto-collect evidence continuously. Instead of manually exporting user lists from AWS IAM monthly, an integration pulls that data automatically. Tools can take automated screenshots of settings on a schedule. Nothing gets missed, and you save dozens of hours.
How Pre-Built Policy Templates Save Time
Drafting policies from scratch can take weeks. Automation software provides pre-written templates covering SOC 2 requirements, and AI can customize them for your company. Input that you're a 20-person AI SaaS handling healthcare data, and the tool adjusts the Incident Response policy accordingly. You review and tweak rather than write from blank.
How Continuous Compliance Monitoring Works
Compliance isn't a one-time checklist. Automation shines here by continuously monitoring your systems and alerting you to drift. If someone creates a public S3 bucket when your policy forbids it, you get flagged immediately. If a new employee hasn't completed security training after X days, you get an alert. This means you fix issues before auditors find them.
How AI-Powered Compliance Assistants Help
New platforms often include AI assistants that answer compliance questions instantly. Not sure how to properly encrypt database backups? The assistant provides best practices and points to the right setting. AI can also help with security questionnaires from customers, auto-generating answers by referencing your compliance program.
How Much Time Can You Save with Automation?
With automation, many startups have slashed preparation from months to weeks (or even days). Instead of 200 hours of grunt work, your team might spend 20 hours reviewing while software handles the rest.
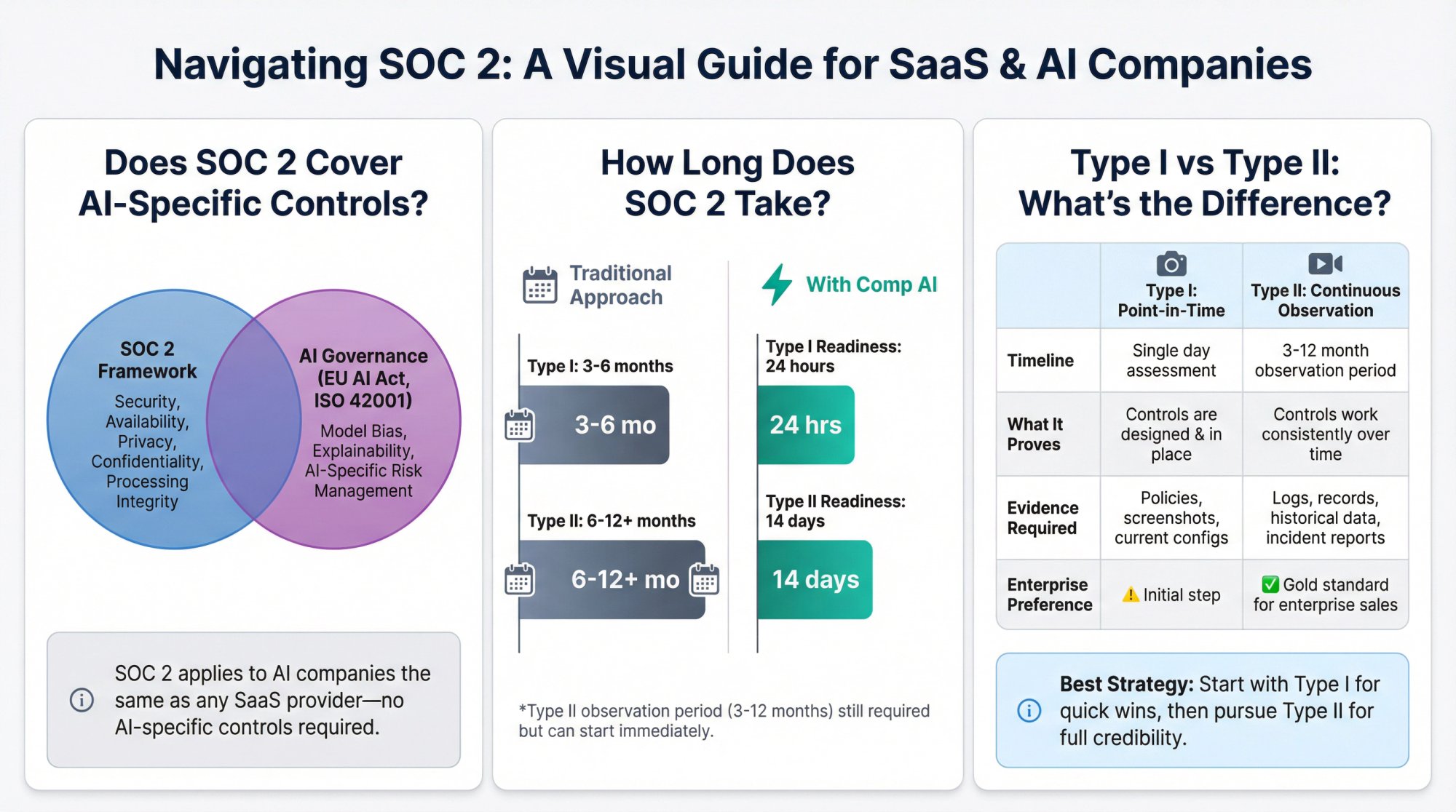
Price with Comp AI: $5,000-10,000 Price with others: $15,000+
Consider the math: traditional approaches (consultant + legacy platform + auditor + internal time) can easily cost $20K-30K or more. Modern automated platforms offer the same outcome at a fraction of the cost and time.
How Comp AI Helps AI Companies Get SOC 2 (In Days, Not Months)
Comp AI is an AI-driven compliance automation platform particularly well-suited for AI companies that need SOC 2 done fast without sinking tons of resources.
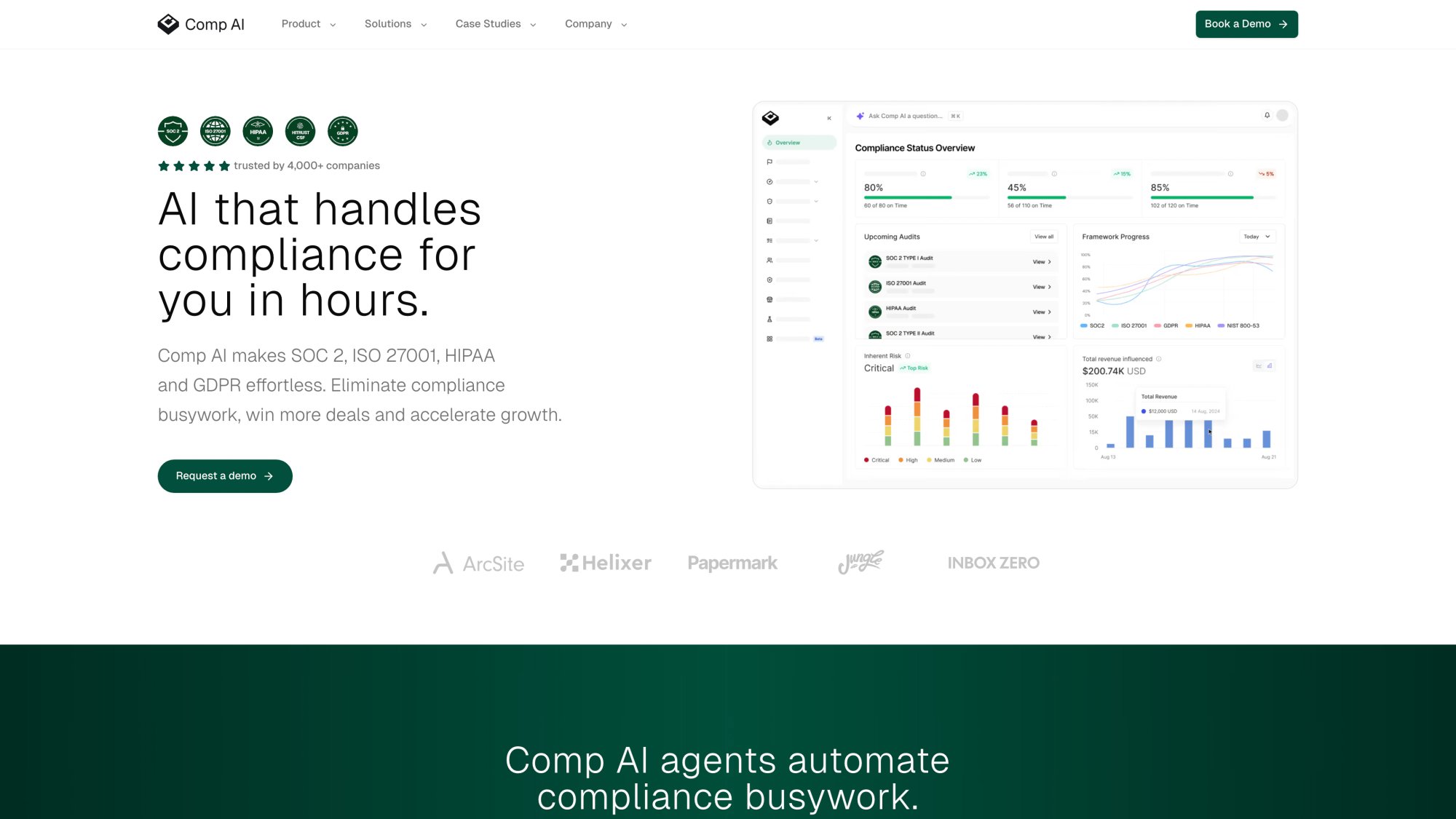
How Comp AI Achieves Lightning-Fast SOC 2 Readiness
Comp AI's workflow combines intelligent automation with expert support to compress timelines dramatically. SOC 2 Type I audit readiness in 24 hours isn't a typo. If your company is motivated, you can gather all needed policies and evidence in as little as a day. (Compare that to the 3+ months it traditionally takes without such tools.)
For SOC 2 Type II, Comp AI targets audit readiness in approximately 14 days. That means getting all controls implemented and verified so you can start the required observation period immediately.
How Comp AI's Automation Actually Works
Comp AI uses AI agents to handle compliance busywork. Upon onboarding, these agents connect to your systems and start hunting for evidence: pulling configuration data, user lists, security settings, and taking screenshots autonomously. If an S3 bucket is misconfigured, the AI flags it and can suggest the fix in code.
Importantly, Comp AI's team built guardrails around the AI to ensure accuracy. Early on, they learned to validate AI-collected evidence to avoid hallucinations. The result: 95%+ of evidence collection and analysis is automated, with human verification on critical items.
How Comp AI Handles Policy Setup for You
Rather than handing you template libraries and wishing you luck, Comp AI provides white-glove service. The platform's AI generates all required policies (InfoSec, Access Control, Incident Response, etc.) tailored to your tech stack. Then compliance experts review and fine-tune them with you.
You go from zero to a full set of audit-ready policies in days, not the typical month of drafting and revisions.
How Comp AI's Trust Center Accelerates Sales
Comp AI includes a real-time Trust Center: a public-facing security portal where you can showcase your SOC 2 (and other certs) to customers. The portal is AI-enhanced, so it can automatically answer security questionnaire questions by pulling from your actual controls and policies.
For AI companies selling to enterprises, this turns compliance from a blocker into an accelerator. You maintain control (you can review answers), but the burden lifts dramatically.
How Comp AI Provides Expert Support
Despite heavy automation, Comp AI doesn't leave you alone. They provide 1:1 support via Slack with compliance experts who understand AI businesses. Have a question about how SOC 2 applies to your ML data pipeline? Need guidance on best practices for cloud GPU security? Real experts respond in real-time.
How Much Does Comp AI Cost?
Traditional compliance approaches cost $20K-30K or more when you add software fees, auditor costs, and internal time. Comp AI positions itself as significantly more affordable.
Price with Comp AI: $5,000-10,000Price with others: $15,000+
Comp AI offers packages covering both platform and audit at a flat rate with no hidden fees. If you don't pass your audit, you get refunded. (With a 100% success rate, that rarely happens.)
Is Comp AI Ready for Future AI Governance?
Comp AI already supports 25+ compliance frameworks (SOC 2, ISO 27001, HIPAA, GDPR, and more). As AI governance frameworks like the EU AI Act or ISO 42001 become relevant, you'll manage multiple compliance needs in one place rather than starting from scratch.
Real Results from AI Companies Using Comp AI
"We were only 30-40% of the way through SOC 2 with \[another platform\] after 4 months. We switched to Comp AI, and they had us audit-ready in a couple of days." - CTO, Persona AI
That kind of acceleration can mean the difference between losing a deal due to compliance delays and closing it on time.
Frequently Asked Questions About SOC 2 for AI Companies
Does SOC 2 Have Any AI-Specific Requirements?
No. SOC 2 does not contain any controls unique to artificial intelligence or machine learning systems. It applies to AI companies the same way it applies to any cloud or software provider that handles customer data. The framework focuses on security, availability, processing integrity, confidentiality, and privacy of data and systems. It won't ask about model bias, ML explainability, or AI-specific governance. Those topics may be addressed by emerging frameworks like the EU AI Act or ISO 42001, but they're outside SOC 2's scope.
How Long Does It Take to Get SOC 2 Compliant?
It depends on your approach. Traditional methods (DIY with spreadsheets, basic tools, consultants) typically take 3-6 months for Type I and 6-12+ months for Type II. With modern automation platforms like Comp AI, companies have achieved Type I audit readiness in as little as 24 hours and Type II readiness in about 14 days. The actual Type II audit period still requires 3-12 months of observation, but you can start that period much sooner.
What's the Difference Between SOC 2 Type I and Type II?
Type I is a point-in-time assessment. It asks: "As of today, do you have the required security policies and controls in place?" It proves you've designed appropriate controls but doesn't prove they work consistently.
Type II evaluates your controls over a period (typically 3-12 months). The auditor verifies you actually follow your policies in practice, reviewing evidence of continuous compliance. Type II is considered the gold standard because it demonstrates operational effectiveness. Most enterprise customers ultimately want to see a Type II report.
How Much Does SOC 2 Compliance Cost for AI Startups?
Costs vary widely based on your approach:
- DIY with consultants: $20,000-50,000+ (software, auditor fees, consultant time, internal hours)
- Legacy compliance platforms: $15,000-30,000+ (platform fees typically $10K-20K plus auditor)
- Price with Comp AI: $5,000-10,000
- Price with others: $15,000+
Comp AI offers all-in packages (platform + audit) at a flat rate, making budgeting predictable.
Can a Small AI Startup with No Compliance Team Get SOC 2?
Absolutely. Many Comp AI customers are small startups (sometimes just 2-3 people) with no dedicated compliance personnel. That's exactly why platforms with done-for-you services exist. Comp AI's AI handles evidence collection, generates policies tailored to your setup, and their compliance experts guide you through anything you can't automate. You don't need to hire a compliance officer or vCISO if you use the right platform.
Do I Need SOC 2 If I Already Have ISO 27001?
SOC 2 and ISO 27001 are different frameworks with different audiences. ISO 27001 is an international standard more common in Europe and for companies with global operations. SOC 2 is an American standard particularly expected by U.S. enterprises. Many companies pursue both, especially if they sell to both U.S. and international customers. The controls overlap significantly (around 60-70%), so having one makes achieving the other easier. Comp AI supports both frameworks, letting you manage compliance for each in a unified platform.
How Often Do You Need to Renew SOC 2?
SOC 2 reports are generally valid for 12 months. You'll need to undergo annual Type II audits to maintain compliance. Some enterprise customers may accept a Type I report initially but will eventually require a current Type II. Building continuous compliance habits (rather than treating it as an annual crunch) makes renewals much smoother.
How AI Startups Can Build Trust at Speed
For AI companies, SOC 2 compliance isn't just a certificate to hang on the wall. It's about building trust in an era where customers rightfully question how their data gets handled, especially by AI systems they can't fully see inside.
The journey to SOC 2 might seem intimidating at first glance. But with the right approach, even a small AI startup can go from zero to SOC 2 in weeks rather than quarters.
Key takeaways:
- Start with the "why." SOC 2 will significantly bolster your startup's trustworthiness and unlock new opportunities. Viewing it as an investment (rather than a chore) helps get team buy-in.
- Work smarter, not harder. Don't reinvent the wheel. Use templates, follow proven steps, and seriously consider compliance automation platforms. In 2025, manual compliance is like writing code without an IDE.
- Focus on culture, not just checkboxes. Embrace the spirit of SOC 2 by integrating security best practices into daily operations. Train your team, enforce good habits, and treat your compliance as an ongoing commitment to excellence.
- Use compliance as a selling point. Once you have that SOC 2 report, put it to work. Feature it on your website, share it proactively in sales conversations, set up a trust center. Compliance can differentiate you from competitors who aren't there yet.
Time is often of the essence for AI startups. Whether it's a major customer waiting on security clearance or an investor doing due diligence, being able to deliver a SOC 2 report (or at least show a credible path to one) can make or break key moments.
With platforms like Comp AI, you have the option to pursue compliance at startup speed. Accomplishing in days what used to take months. Without sacrificing rigor or accuracy. And without derailing your product roadmap.
In the world of artificial intelligence, innovation moves fast. Your approach to security and compliance should keep pace. SOC 2 for AI companies is absolutely achievable. Start early, do it right, and you'll build the trust foundation that lets your AI venture scale.
This guide reflects SOC 2 practices and compliance landscape as of 2025. As security requirements evolve, AI companies should stay updated on new standards and continuously improve their controls.