Continuous Compliance Monitoring: Guide (2025)
Learn how continuous compliance monitoring keeps you audit-ready 24/7. Save hundreds of hours and close deals faster with real-time visibility.
Getting that SOC 2 or ISO 27001 certification feels like crossing a finish line. Your team worked hard, gathered mountains of evidence, and finally got that report in hand. But here's what nobody tells you on certification day: compliance isn't a destination. It's more like a gym membership where you actually have to keep showing up.
The moment your auditor signs off, your compliance posture starts drifting. New employees join without completing security training. Someone spins up an AWS instance without following proper protocols. A vendor changes their security practices. And suddenly, that certification you worked so hard for doesn't reflect your actual security state anymore.
This is where continuous compliance monitoring changes everything. Instead of scrambling before your next audit, you stay audit-ready all the time. Instead of discovering compliance gaps months after they happen, you catch them in real time. And instead of treating compliance as a dreaded annual project, it becomes a quiet background process that just works.
In this guide, we'll break down exactly what continuous compliance monitoring means, why it's become essential for modern companies, and how to implement it without burning out your team.
What Is Continuous Compliance Monitoring and How Does It Work?
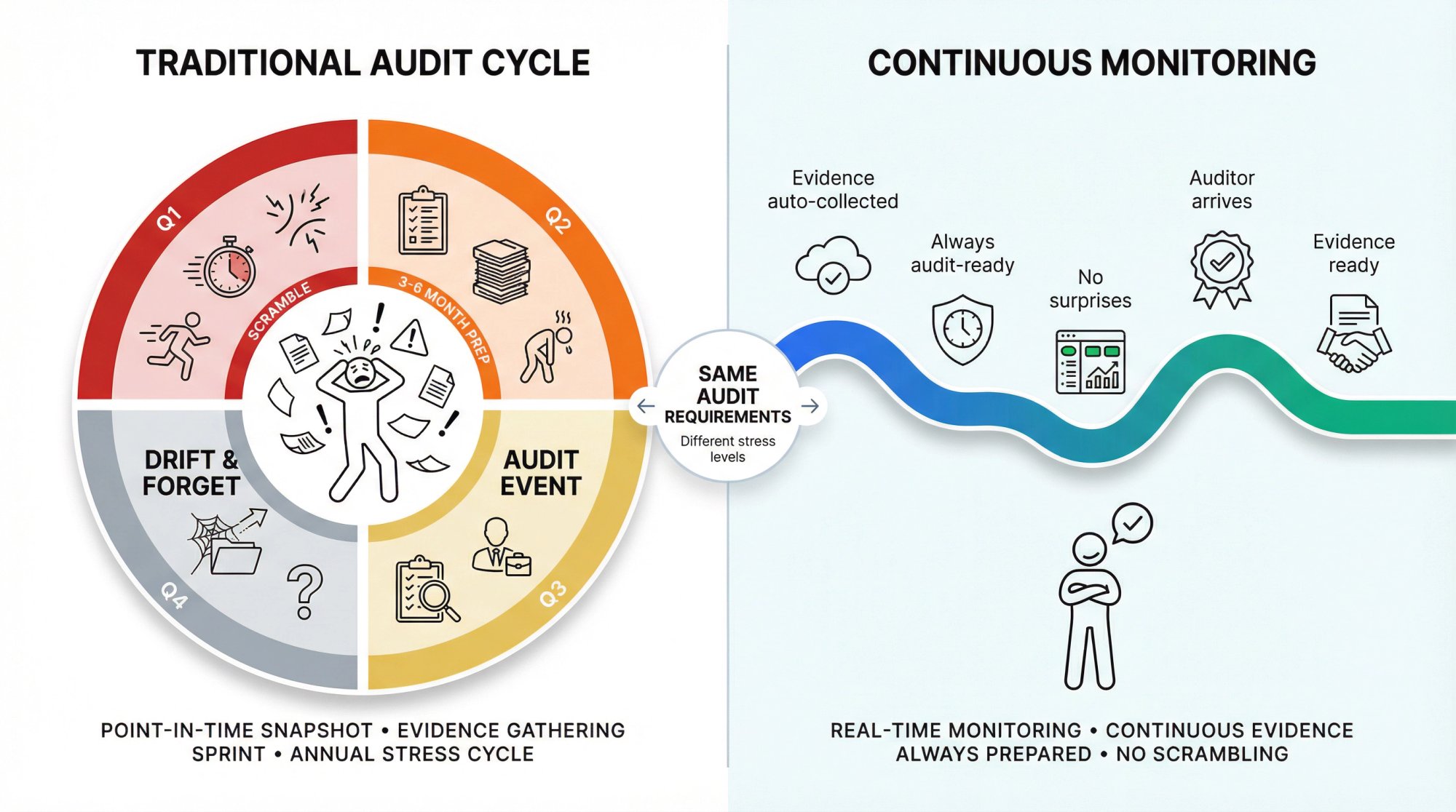
Continuous compliance monitoring is exactly what it sounds like: an ongoing, automated approach to tracking and maintaining your compliance posture. Rather than treating compliance as a point-in-time snapshot (like traditional audits), continuous monitoring treats it as a constant state that gets verified around the clock.
Think of it this way. Traditional compliance is like getting a health checkup once a year. You might pass with flying colors, but a lot can change in 12 months. Continuous compliance monitoring is more like wearing a fitness tracker that alerts you the moment something needs attention.
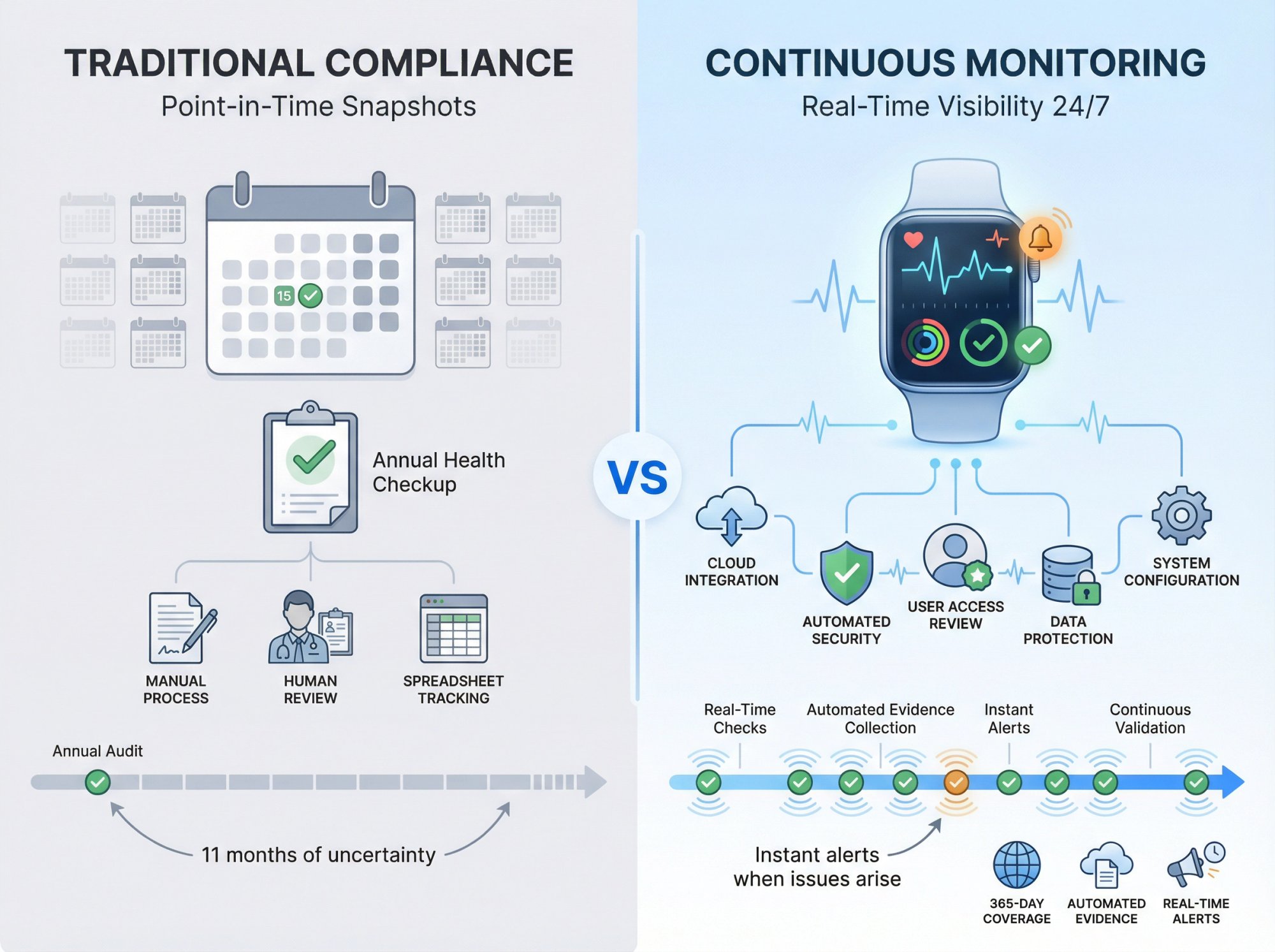
In practice, continuous compliance monitoring combines automated evidence collection, real-time alerting, and ongoing policy management into a single system. Your cloud infrastructure gets scanned daily (or even hourly). Employee security training completion gets tracked automatically. Access reviews happen on schedule without someone manually chasing down approvals. Configuration changes get flagged the moment they drift from your baseline.
The result? You always know your compliance status. No surprises during audits. No late-night evidence-gathering sprints. Just steady, predictable compliance that runs in the background while you focus on building your business.
Why Annual Compliance Audits Are No Longer Enough
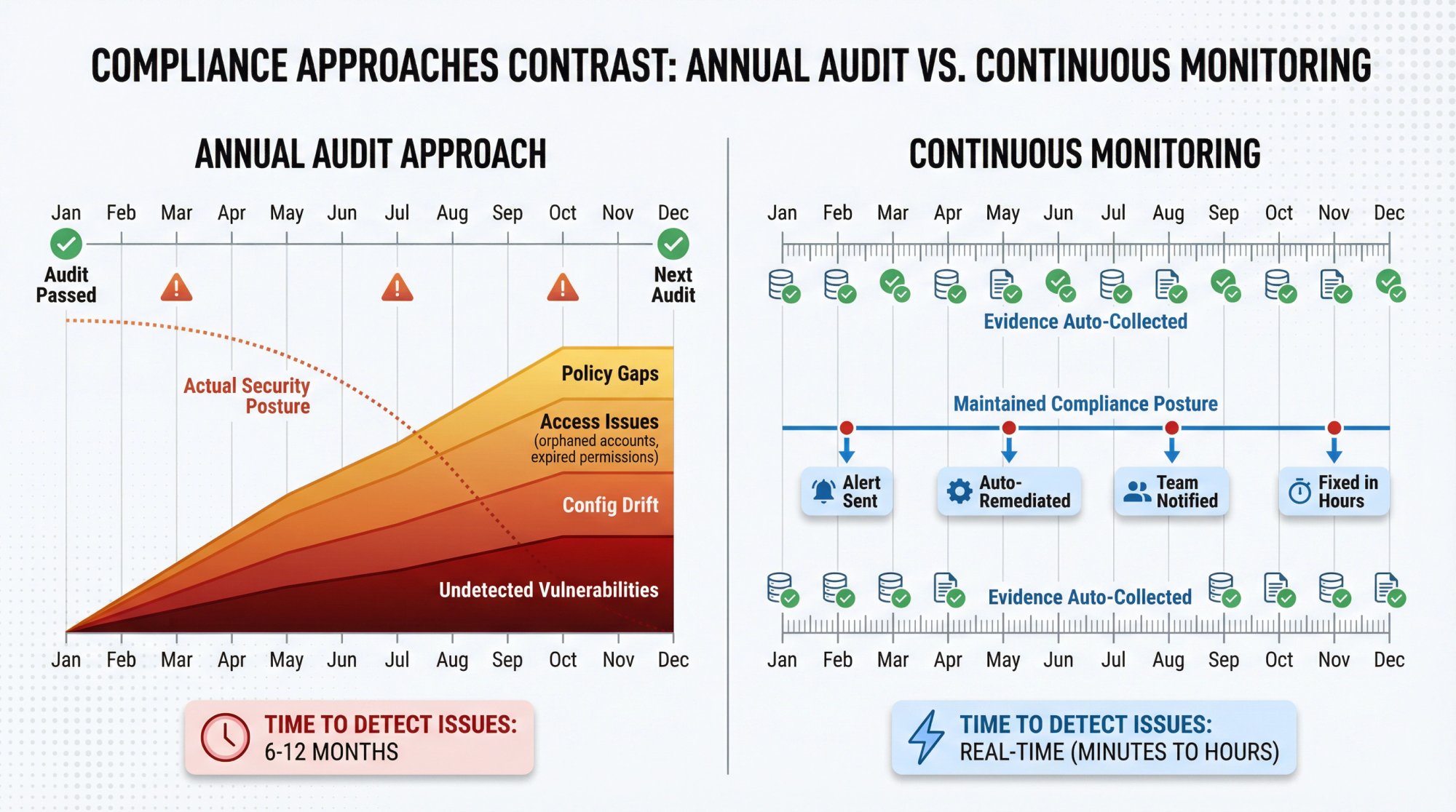
For years, the standard approach to compliance looked something like this: spend three to six months preparing for an audit, gather all your evidence in a frantic push, pass the audit, then mostly forget about it until next year. This "audit sprint" model made sense when technology moved slower and regulatory requirements were simpler.
But the world has changed. Here's why the old approach creates real problems:
Security gaps grow undetected. Between audits, your actual security posture drifts from what you documented. New vulnerabilities emerge. Configurations change. People leave the company with access still active. By the time your next audit rolls around, you're essentially starting from scratch to figure out where things stand.
Customer expectations have evolved. Enterprise buyers don't just want to see a SOC 2 report from six months ago. They want to know your security posture right now. Trust portals and real-time compliance dashboards have become standard expectations. If you can't show continuous monitoring, you look behind the times.
Framework requirements keep growing. SOC 2, HIPAA, ISO 27001, GDPR, PCI DSS, and others all have overlapping but distinct requirements. Managing these manually across multiple frameworks is practically impossible. The administrative overhead alone can consume a full-time employee.
Audit costs compound. When you're not continuously compliant, every audit requires a massive preparation effort. That means more consultant fees, more internal hours, and more stress. Companies that monitor continuously spend a fraction of the time and money on audit prep because there's nothing to "prepare" when you're always ready.
The bottom line: point-in-time compliance was designed for a slower era. Modern security demands continuous visibility, and the companies that understand this gain a serious competitive advantage.
What Are the Core Components of Continuous Compliance Monitoring?
Building a continuous compliance program isn't about buying a single tool and flipping a switch. It's about putting systems in place that work together to maintain your compliance posture automatically. Here are the core components that make it work.
How Does Automated Evidence Collection Save Time?
Evidence collection is where most compliance teams spend the bulk of their time. You need screenshots of configurations, exports of user lists, proof of encryption settings, logs showing access reviews were completed, and dozens (sometimes hundreds) of other artifacts.
Automated evidence collection connects directly to your systems and pulls this information without human intervention:
→ Your AWS, Azure, or GCP configurations get scanned and documented
→ Your identity provider exports user lists and access logs
→ Your HR system tracks who completed security training
→ Your code repositories show branch protection settings and vulnerability scans
The beauty of automation is that it doesn't just save time once. It saves time continuously. Every day, every week, every month, the evidence keeps collecting itself. When audit time comes, you're not hunting down 200 screenshots. You're exporting a pre-organized bundle that your auditor can review immediately.
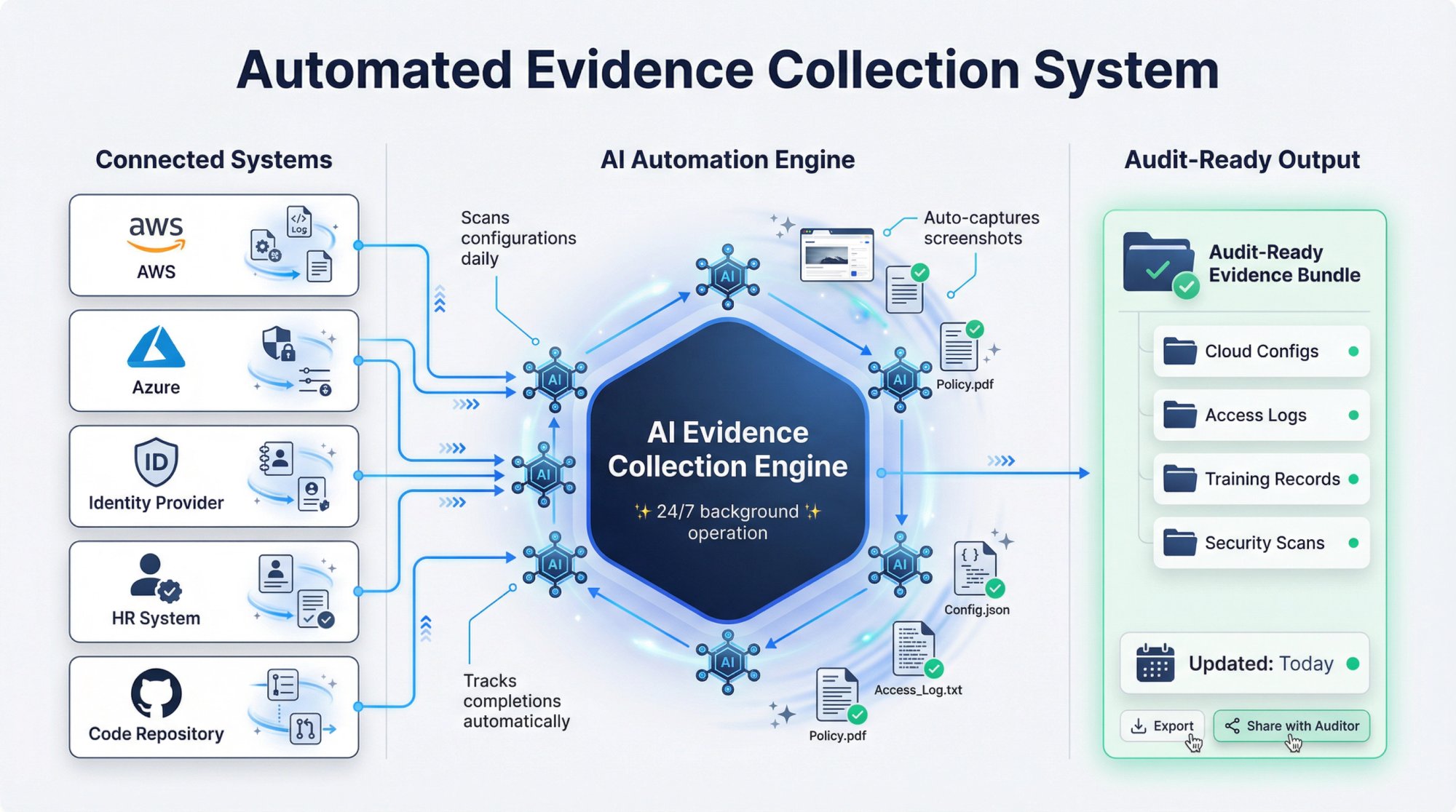
At Comp AI, our AI agents actively hunt for evidence across your connected systems, take screenshots, and document controls automatically. This turns weeks of manual evidence gathering into something that happens in the background while you sleep.
What Alerts and Notifications Should Continuous Monitoring Include?
Continuous monitoring means nothing if problems go unnoticed. Real-time alerting ensures that when something drifts out of compliance, the right people know immediately.
Control failure detection catches issues like:
- Someone disabling MFA on a critical account
- An S3 bucket getting set to public
- Encryption being turned off on a database
- A user being granted admin access without proper approval
These aren't just security problems. They're compliance failures that could show up in your next audit.
Drift monitoring compares your current state against your documented baseline and flags differences. Maybe your backup retention policy says 30 days, but someone changed a setting to 7 days. Drift monitoring catches that before it becomes an audit finding.
Smart alerting also means not overwhelming people with noise. Good continuous monitoring systems let you configure severity levels and routing so that critical issues get immediate attention while minor items get batched into daily summaries.
How to Keep Security Policies Updated Automatically
Your security policies aren't static documents that sit in a Google Drive folder forever. They need to evolve as your company grows, as regulations change, and as new threats emerge.
Continuous policy management treats your policies as living documents with proper version control and audit trails. When a policy changes, you can see who changed it, when, and why. You can track which version was in effect during any given audit period.
Modern compliance automation platforms also generate and update policies automatically. Instead of starting from scratch with a blank document, you get AI-generated drafts customized to your technology stack and business context. Need an Access Control policy that mentions your specific identity provider? Need an Incident Response plan that matches your actual escalation procedures? Automation handles the heavy lifting.
Why Compliance Dashboards Matter for Your Team
Visibility is the foundation of continuous compliance. If you can't see your compliance status at a glance, you can't manage it effectively.
A compliance dashboard shows you exactly where you stand across all your frameworks. Which controls are passing? Which are failing? Where are the gaps? What needs attention this week?
For executives and board members, dashboards provide the oversight they need without diving into technical details. For compliance managers, they're the command center for daily operations. For auditors, they're proof that continuous monitoring is actually happening.
Good dashboards also generate reports on demand. Need to show a prospective customer your SOC 2 readiness? Export a summary. Need to demonstrate your HIPAA posture to a healthcare partner? Pull a compliance scorecard. This kind of real-time reporting has become a sales asset, not just an administrative requirement.
What Are the Benefits of Continuous Compliance Monitoring?
Here's what continuous compliance monitoring actually delivers in practical terms.
Dramatic time savings. Companies using automated continuous monitoring report saving hundreds of hours per year on compliance activities. What used to be a three-month audit prep cycle becomes a few days of final review. What used to be weekly manual evidence checks becomes something that happens automatically.
| Metric | Traditional Approach | With Continuous Monitoring |
|---|---|---|
| Annual compliance costs | $50,000+ (consultants + internal hours) | $5,000-10,000 (platform costs) |
| Audit prep time | 3-6 months | Days of final review |
| Evidence collection | Manual weekly checks | Automated, continuous |
| Time to identify drift | Discovered at audit | Real-time alerts |
Platforms like make these cost reductions possible through end-to-end automation.
Reduced audit stress and costs. When you're always audit-ready, audits stop being emergency events. Your auditor can pull evidence any time because it's always current. There's no scrambling to recreate documentation or explain gaps. Audit costs drop because there's simply less work to do.
Improved security posture. Here's something people don't always expect: continuous compliance monitoring actually makes you more secure, not just more compliant. When configuration issues get flagged in real time, you fix them before they become vulnerabilities. When access reviews happen consistently, you don't have orphaned accounts sitting around for attackers to exploit.
Faster sales cycles. Enterprise deals often stall on security reviews. "Do you have SOC 2?" "Can you fill out this 200-question security questionnaire?" "Can we see your security policies?" With continuous monitoring and a real-time trust center, these questions get answered in minutes instead of days. Some Comp AI customers have reported closing deals worth hundreds of thousands of dollars that would have been lost to compliance delays.
Better risk management. Continuous monitoring gives you visibility into risks you didn't even know existed. Maybe you assumed all your databases were encrypted, but monitoring reveals one that got missed. Maybe you thought all vendors completed their security reviews, but the data shows three are overdue. Understanding third-party risk management and having a proper vendor risk policy becomes much easier with automated tracking.
Multi-framework efficiency. If you need SOC 2, HIPAA, ISO 27001, and GDPR, continuous monitoring lets you map controls across frameworks once and maintain them together. Many controls overlap, so satisfying one framework often satisfies parts of others. Understanding the differences between frameworks like ISO 27001 vs SOC 2 helps you plan this strategy. This "control mapping" approach can reduce overall compliance effort by 40% or more for companies maintaining multiple certifications.
How Comp AI Automates Continuous Compliance Monitoring
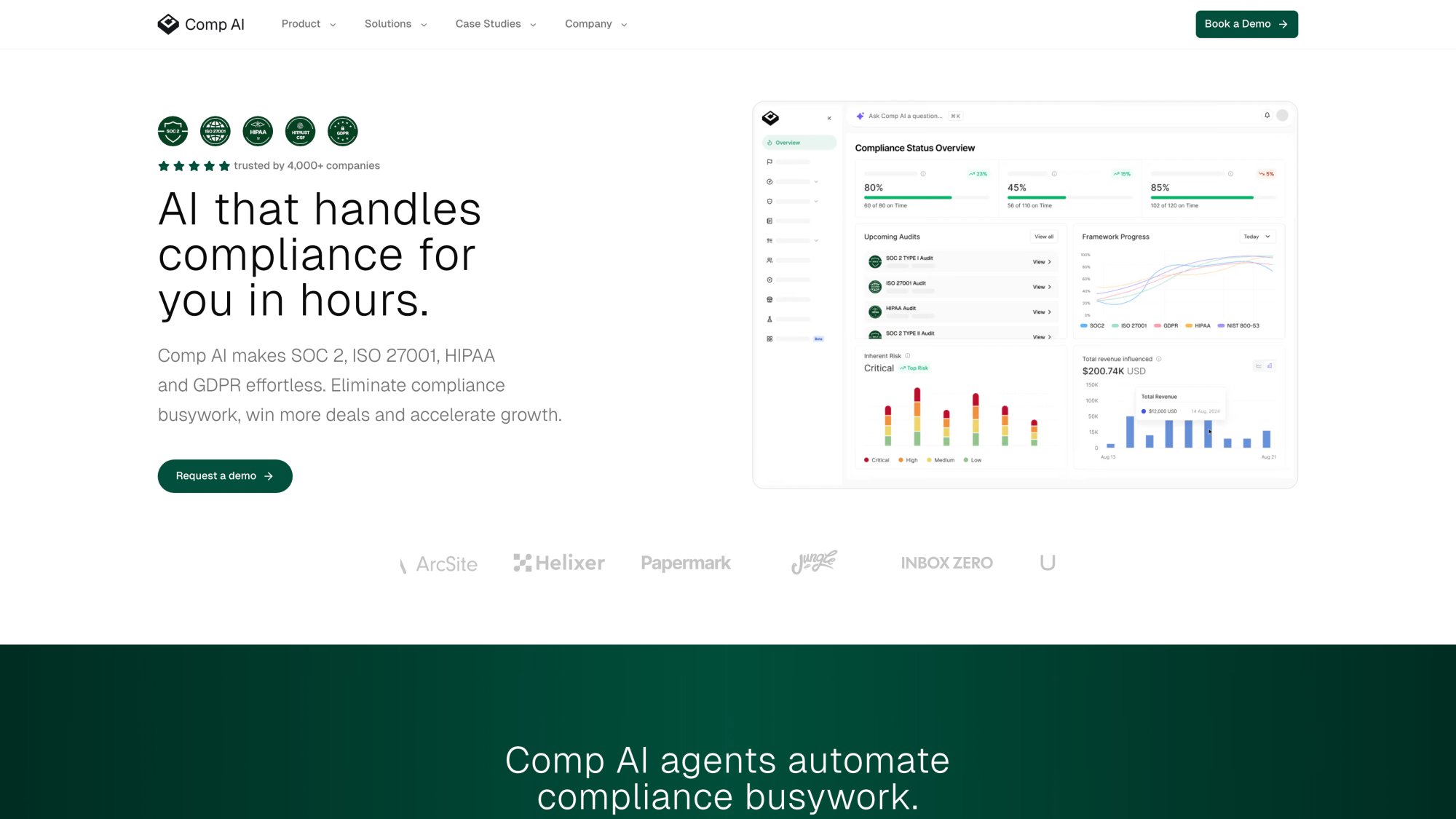
At Comp AI, we built our platform specifically for continuous compliance monitoring. Here's what that looks like in practice:
AI agents that never sleep. Our autonomous AI agents monitor your connected systems around the clock. They collect evidence, check configurations, flag drift, and document everything automatically. You're not logging in to manually verify that MFA is still enabled on your identity provider. Our agents do that verification daily and alert you if anything changes.
100+ integrations for complete coverage. Continuous monitoring only works if it covers your actual tech stack. We integrate with major cloud providers (AWS, Azure, GCP), identity providers, HR systems, code repositories, endpoint management tools, and more. Evidence collection happens across your entire environment, not just the parts that are easy to connect.
Automated policy generation. Don't have security policies yet? Our AI generates them based on your setup. Already have policies? Our system keeps them updated as your environment changes. Version control and audit trails come built in.
Real-time trust center. Share your compliance posture with customers and partners through a public-facing trust center. They can see your certifications, download policies (with appropriate access), and even check your real-time compliance status. This turns compliance from a sales blocker into a sales accelerator.
Dedicated support via Slack. Continuous monitoring is technology, but compliance still has a human element. Our team provides direct Slack support with fast response times. When you have a question about a control or need guidance on a requirement, you get expert answers without scheduling calls or waiting days for email responses.
We stand behind our approach. That's how confident we are in continuous compliance done right.
Customers like Persona AI have experienced this firsthand. After spending four months with another platform and only reaching 30-40% SOC 2 readiness, they switched to Comp AI and reached audit-ready status in just a couple of days. That's the difference continuous, AI-powered compliance monitoring makes.
How to Implement Continuous Compliance Monitoring (Step-by-Step)
Ready to make the switch from point-in-time to continuous? Here's a practical roadmap:
Step 1: Assess your current state.
Before implementing continuous monitoring, understand where you're starting. What frameworks do you need to comply with? What systems contain compliance-relevant data? What's your current compliance posture? A SOC 2 readiness assessment establishes this baseline and prioritizes your efforts.
Step 2: Choose your frameworks strategically.
Most companies start with SOC 2 because it's the most commonly requested security certification for B2B software. If you're wondering how to get SOC 2 certification, the process is simpler than many expect with the right automation. From there, HIPAA (if you handle health data), ISO 27001 (for international credibility), or GDPR (for European operations) often follow. Choose based on what your customers and market require.
Step 3: Connect your systems.
Continuous monitoring requires visibility. Connect your cloud infrastructure, identity provider, HR system, and other critical tools to your compliance platform. The more connected you are, the more automated your evidence collection becomes.
Step 4: Establish your control baseline.
Document your current controls and configurations as your baseline. This becomes the reference point for drift detection. If something changes from this baseline, you'll know about it. A detailed SOC 2 compliance checklist guides this process.
Step 5: Configure alerting.
Set up notifications so the right people hear about the right issues. Critical control failures might go to your security team immediately. Minor drift might get batched into weekly reports. Finding this balance prevents alert fatigue while ensuring nothing important gets missed.
Step 6: Run your first audit cycle.
Your first audit with continuous monitoring will still take some effort because you're establishing processes. But you'll notice immediately how much easier evidence collection is. Each subsequent audit gets faster.
Step 7: Measure and optimize.
Track metrics like time-to-remediation for compliance issues, percentage of controls passing, and hours spent on compliance activities. Use this data to continuously improve your program.
With Comp AI, most companies complete this entire setup in days, not months. Our onboarding team handles integration configuration and policy customization so you can focus on running your business.
Continuous Monitoring Requirements for SOC 2, HIPAA, and ISO 27001
Different frameworks have different requirements, but continuous monitoring principles apply across all of them. Here's what to know about the major frameworks:
| Framework | Focus Area | Key Monitoring Requirements | Typical Timeline |
|---|---|---|---|
| SOC 2 | Trust Services Criteria | Access controls, change management, incident response | Type I: 24 hours; Type II: 3-12 months |
| HIPAA | Protected Health Information | PHI access logs, encryption, workforce training | 7 days to audit-ready |
| ISO 27001 | Information Security Management | Risk assessments, control implementation, continual improvement | 14 days to audit-ready |
What Does SOC 2 Continuous Monitoring Require?
SOC 2 evaluates your controls across five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Understanding the full SOC 2 compliance requirements is essential for effective monitoring. Continuous monitoring for SOC 2 focuses on:
- Access controls and user provisioning/deprovisioning
- Change management and deployment processes
- Incident detection and response capabilities
- Data encryption in transit and at rest
- Vendor management and third-party risk
- Business continuity and backup procedures
For SOC 2 Type I vs Type II, the distinction matters for continuous monitoring. Type II (which requires demonstrating controls over a period of time) is especially valuable with automated monitoring. You need to show that controls worked consistently over your observation period, typically three to twelve months. Automated monitoring provides the ongoing evidence you need.
What Are HIPAA Continuous Monitoring Requirements?
HIPAA compliance revolves around protecting Protected Health Information (PHI). Use a HIPAA compliance audit checklist to ensure your monitoring covers all requirements. Continuous monitoring for HIPAA emphasizes:
- Access logs for systems containing PHI
- Encryption status for PHI at rest and in transit
- Workforce security training completion
- Business Associate Agreement tracking
- Incident response and breach notification readiness
- Device and endpoint security for anything accessing PHI
Healthcare organizations face serious consequences for HIPAA violations, making continuous monitoring more than a convenience. Real-time visibility into PHI access and security controls can be the difference between catching a potential breach early and facing OCR enforcement action.
What Does ISO 27001 Continuous Monitoring Include?
ISO 27001 takes a risk-based approach to information security management. Understanding the full ISO 27001 certification requirements enables effective continuous monitoring. The ISO 27001 certification process covers:
- Risk assessment and treatment status
- Control implementation across the Annex A requirements
- Internal audit schedules and findings
- Management review activities
- Corrective action tracking
- Continual improvement documentation
ISO 27001 requires an Information Security Management System (ISMS) that's actively maintained. Continuous monitoring tools can serve as the operational backbone of your ISMS, ensuring requirements are consistently met rather than just documented.
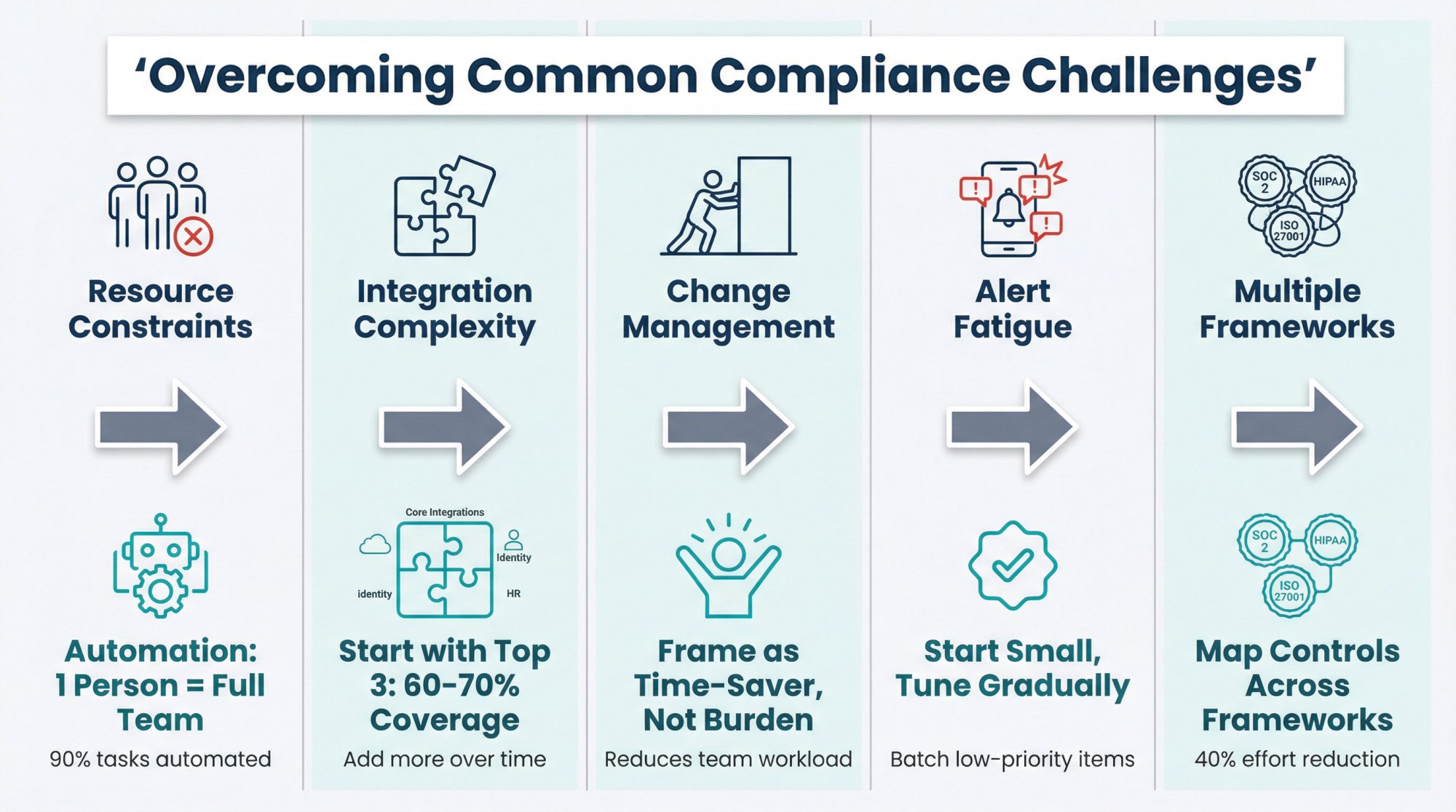
How to Overcome Common Continuous Compliance Challenges
Implementing continuous compliance monitoring isn't without obstacles. Here are the most common challenges and how to address them:
Challenge: Resource constraints.Many teams worry they don't have enough people to implement and maintain continuous monitoring. The solution is choosing tools that minimize manual overhead. Automated compliance software automates up to 90% of compliance tasks, meaning you don't need a dedicated compliance team to run an effective program. One person can manage what used to require several.
Challenge: Integration complexity.
Your tech stack might include dozens of tools, and connecting them all feels overwhelming. Start with your highest-impact integrations: cloud provider, identity provider, and HR system. These typically cover 60-70% of your compliance evidence needs. Add other integrations over time as you identify gaps.
Challenge: Change management.
Continuous monitoring changes how teams work. Developers might push back against security gates in their deployment pipeline. HR might resist new procedures for onboarding documentation. Address this by framing continuous compliance as a time-saver, not a burden. When people see that automation reduces their workload, resistance fades.
Challenge: Alert fatigue.
Without proper tuning, continuous monitoring can flood teams with notifications. Combat this by starting with fewer, more important alerts and expanding gradually. Batch low-priority issues into digests. Route different alert types to different people based on responsibility. Most importantly, fix root causes rather than just acknowledging alerts so the noise decreases over time.
Challenge: Maintaining multiple frameworks.
If you need SOC 2, HIPAA, and ISO 27001, the control overlap can feel confusing. Use a platform that maps controls across frameworks so you satisfy multiple requirements with single implementations. Comp AI supports 25+ frameworks with built-in control mapping, so maintaining multiple certifications becomes manageable.
Frequently Asked Questions
What is continuous compliance monitoring?
Continuous compliance monitoring is an automated approach to maintaining your compliance posture around the clock. Instead of preparing for audits once a year, you use connected tools to track your compliance status constantly, collecting evidence automatically and alerting you to issues in real time.
How often does continuous monitoring collect evidence?
This varies by control type and risk level. Critical security configurations might be checked hourly. User access lists might be pulled daily. Training completion might be tracked weekly. Good continuous monitoring systems let you configure frequency based on your needs.
What frameworks support continuous monitoring?
All major compliance frameworks benefit from continuous monitoring. SOC 2, HIPAA, ISO 27001, GDPR, PCI DSS, NIST, FedRAMP, and others all have controls that can be automated. The specific tools and integrations needed vary by framework, but the continuous monitoring approach applies universally.
How much does continuous compliance monitoring cost?
For a detailed breakdown, see our SOC 2 cost breakdown guide. Platforms like Comp AI start at $3,000-8,000 per year for full platform access, compared to $20,000-50,000+ with traditional approaches using consultants and manual processes.
The investment in continuous monitoring typically pays for itself within the first audit cycle through reduced preparation time and consultant costs.
How long does it take to implement continuous compliance monitoring?
With modern platforms, initial setup happens in days. Most Comp AI customers go from signup to audit-ready in under two weeks, with some achieving readiness in 24-48 hours depending on their starting point. Traditional implementation without automation can take three to six months. Our SOC 2 timeline calculator estimates your specific timeline.
What integrations are needed for continuous compliance monitoring?
At minimum, you'll want to connect your cloud infrastructure (AWS, Azure, GCP), identity provider (Okta, Google Workspace, Azure AD), and HR system. Beyond that, connecting code repositories, endpoint management, and other security tools provides more complete coverage. Most platforms offer 50+ integrations out of the box.
Can continuous monitoring replace audits?
No, but it makes audits dramatically easier. You still need third-party auditors to issue SOC 2 reports or certify ISO 27001 compliance. What continuous monitoring does is ensure you're always ready for those audits. Evidence is pre-gathered. Controls are documented. There's nothing to scramble for when the auditor shows up.
Is continuous compliance monitoring only for large companies?
Not at all. In fact, continuous monitoring is especially valuable for smaller companies that can't dedicate full-time staff to compliance. Automation lets a small team manage enterprise-grade compliance programs. This is particularly relevant for SaaS startups pursuing SOC 2.
How to Turn Compliance Into a Competitive Advantage
Compliance used to be a cost center. Something you did because customers required it or regulations demanded it. The goal was to check the box with minimal pain and move on.
That mindset is outdated. Companies that embrace continuous compliance monitoring don't just avoid the pain of point-in-time audits. They turn compliance into a genuine competitive advantage.
When a prospect asks about your security posture, you don't scramble to find documentation. You share a link to your real-time trust center. When a major customer requires SOC 2, you don't lose the deal to a months-long certification process. You show them your current status and close the business.
When regulators increase requirements or new frameworks become standard, you adapt quickly because your infrastructure for continuous monitoring already exists. When your security team wants to improve posture, they have real-time data showing exactly where to focus.
The companies winning in the market today understand that compliance isn't separate from operations. It's woven into how they build, deploy, and maintain their products. Continuous compliance monitoring is the infrastructure that makes this possible.
Comp AI was built to make this transition effortless. Our AI-powered platform handles the complexity of continuous monitoring so you can focus on what you do best: building great products and serving your customers.
Ready to see how continuous compliance monitoring can transform your approach? Book a demo and discover why thousands of companies trust Comp AI to keep them audit-ready 24/7.
Your next audit doesn't have to be a sprint. Let it be just another day.